Working with Modules - Alerts & Incidents
Alerts
Alerts in FortiSOAR are essentially notifications indicating that an attack has been directed at an organization's systems. Alerts are related to events and often contain essential information for addressing the attack by including vulnerabilities and exploits being leveraged by the potential attack.
Alerts Dashboard
The Alerts Dashboard is a collection of graphs and charts showing visual representations of specific incident activity in the module. An example of the collection of graphs and charts that the system can display by default can be Open Alerts By Severity and Alerts By Type as shown in the following image:

You can customize the graph and chart display to meet your individual team or organization's needs. For more information on Dashboards, see the Dashboard, Template, and Widgets chapter.
Incidents
Incidents represent a collection of information discovered during an Incident Response investigation. Incidents are triggered based on the suspicion or confirmation of a security breach. Incidents may be cyber or physical security related.
Incidents in FortiSOAR document vital information related to cybersecurity violations and attacks that threaten the integrity of your systems and/or data. Critical information such as origin points, severity, and source allow SOC users to assess the scope and reliability of breach while tracking various data such as containment and recovery times help teams identify efficiency trends and gaps in efficiency.
Incidents Dashboard
The Incidents Dashboard is a collection of graphs and charts showing visual representations of specific incident activity in the module. An example of the collection of graphs and charts that the system can display by default can be Open Incidents By Severity and Unresolved Incidents By Severity By Type as shown in the following image:

You can customize the graph and chart display to meet your individual team or organization's needs. For more information on Dashboards, see the Dashboard, Template, and Widgets chapter.
Working with Alerts and Incidents
In FortiSOAR, modules have a List View and a Detail View as described in the following sections. Modules that are used for automation, such as Playbooks and Schedules have been described in the other chapters in this guide.
|
|
In this chapter, we have taken the example of the 'Alerts' Module and described how you could work with alerts. You can work the same way with other modules such as 'Incidents.' |
Alerts List View
The Alerts List View shows the user all the existing alerts the current user's teams own and high-level detail about each alert.
To add an alert in FortiSOAR, click Add Alert in the top bar of the Alerts Module to open the Create New Alert form. Fill in the required details the Create New Alert form and click Save to create an alert. If your administrator has configured default values for any fields, then that default value will be displayed in the Create New Alert form. For example, if your administrator has set the default value of the Status field as Open, then when you create a new alert, by default, the Status field is already set as Open.
The Alerts List View displays records that are sorted by modified date/time with the most recently created/edited alert first. You can change the sort order by clicking on the column headers and specifying the sort criterion. For example, you can sort the Created On column to display either the oldest or the most recent created alerts first. Your administrator can also specify fields based on which the records in the module will be sorted by default. For more information on Default Sort, see the Dashboards, Templates, and Widgets chapter.
|
|
From release 7.2.0 onwards, |
You can right-click an alert in the grid view to display the new context menu options that have been added that enable you to copy record details to the clipboard. Copy Row To Clipboard, Copy Column Data To Clipboard and Copy Cell Value To Clipboard are the context menu options that you can use to copy data for a single row, single column, and single cell respectively. These options do not copy a blank row, a blank column, or a blank cell.

The Copy Row To Clipboard option copies the data only for the visible columns of the selected row to the clipboard in the JSON format. JSON format makes it very easy for you to understand the field name and its value. If you want to copy data other than those of the visible columns, then you must make those columns visible by adding them to the grid in the UI. Use the More Options icon (![]() ) to the right of the table header to hide and unhide columns. Visible columns appear with a green tick icon and hidden columns appear with a red cross icon.
) to the right of the table header to hide and unhide columns. Visible columns appear with a green tick icon and hidden columns appear with a red cross icon.
The Copy Column Data To Clipboard option copies the data of the selected column to the clipboard in the newline-separated format.
The Copy Cell Value Clipboard option copies the data of the selected cell to the clipboard.
You can add tags while creating records, enabling you to search for records in FortiSOAR using tags, making tags very useful in searching and filtering records. You can create tags that have a minimum of three characters. You can add special characters and spaces in tags from version 6.4.0 onwards. However, the following special characters are not supported in tags: ', , , ", #, ?, and /. The Tag field gets auto populated based on tags that are already created. Tags are case insensitive; however, if you create two tags with different case, for example, BFA and bfa, FortiSOAR will display results containing both "BFA" and "bfa".
Administrators can also configure grid and relationships templates so that horizontal scrolling in grid views gets enabled, which provides better usability to users in scenarios where the data grids that have a large number of columns. For more information on how to configure templates, see the Dashboards, Templates, and Widgets chapter.
To edit the template for any module, including Alerts, click the Edit Template icon that is present in the upper right-hand corner. For more information on Templates, see Dashboards, Templates, and Widgets chapter.
Searching and Filtering Alerts
Users can search for a specific alerts within the list (grid) view using the following:
- List View Search - enter text in the search field and click on the search icon to search every column in the list view for the data criteria.
-
Filter Search - enter text in the search criteria row underneath the column header or select one or more options from the picklist under the column header. To search the grid whose lookup or pickup fields are not set or empty, you can select the Not Set option from the picklist under the column header. For example, to search for alerts whose 'Status' or 'Type' is not set.
Note: You cannot search or filter encrypted fields.
You can also customize or select system filters by clicking the Filter icon next to the list view search field. Then either enter a filter criterion or select a filter from the drop-down menu from the search criteria row underneath the column header or select column filters to customize a view and click the Save Filter button. Clicking Save Filter opens a Save New Filter Dialog in which you must assign a name to the newly created filter.
For example, in the following image, a filter is being created for alerts whose Severity is Critical.
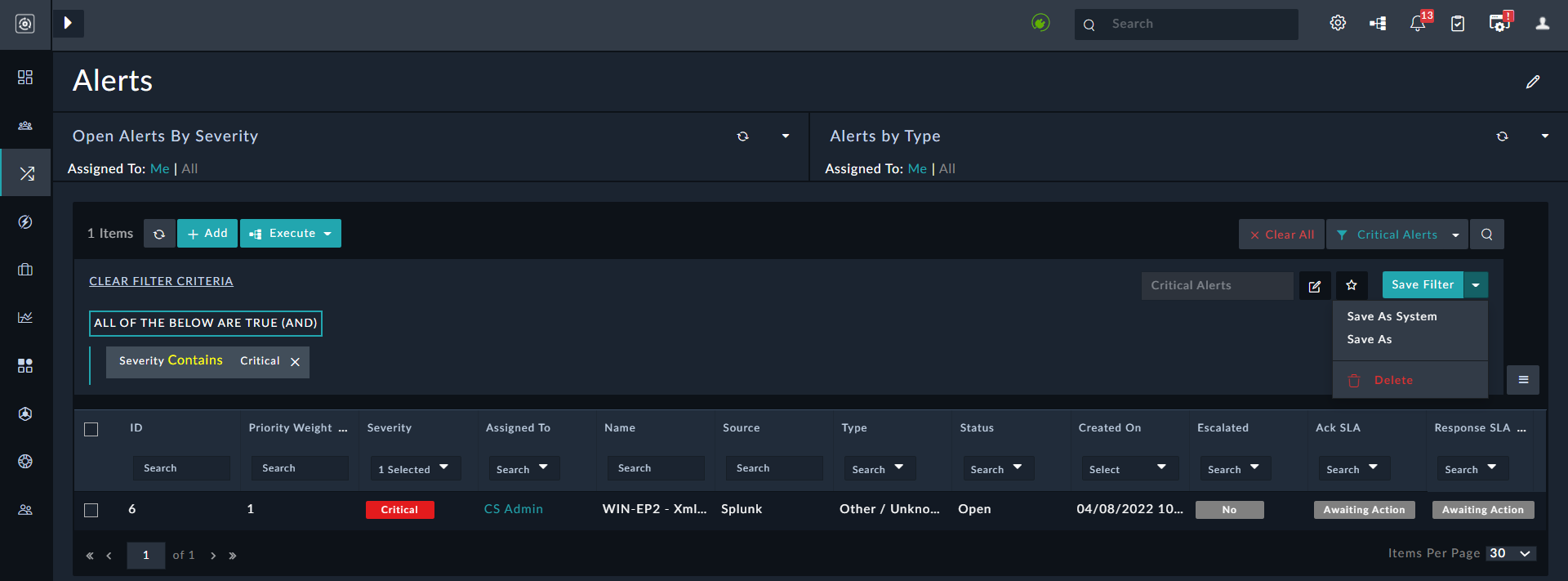
Click Clear All to remove the filter.
You can also define filters for records in the Grid Widget itself. The Grid Widget includes the Nested Filters component that you can use to filter records in the list view using a complex set of conditions, including the OR condition.
See the Searches and Filters and Dashboards, Templates, and Widgets chapters for more information on searching and filtering records.
Exporting Records from the List view
To export records using the grid view, click the More Options icon (![]() ) to the right of the table header:
) to the right of the table header:
-
Export All Columns as CSV: Use this option to export data from all columns, i.e., data from both visible and hidden columns matching the currently set filter (if any) from the alerts grid get exported to a
.csvfile. Also, if you have applied any saved filters then they also get applied while exporting the records. List views of modules have a maximum shown record count of 250 records, which meant that earlier only 250 records could be exported using the other export options available on the More Options menu. When you select this option, theExport All Columns As CSVdialog is displayed, where you can choose to limit the record data being exported.
Select the All records in current page to export data from the records on the current page, or select All records across all pages, to export all the record data.
Important: If you select the All records across all pages option, you must haveCreateandReadpermissions on theFilesmodule andExecuteandReadpermissions on thePlaybooksmodule.
Click Download File to download the CSV file containing the exported records.
-
Export Visible Columns as CSV: Use this option to export visible columns of the alert record to a
.csvfile. The visible columns appear with a green tick icon.
Note: You can hide columns by deselecting a column from the list of columns present within the More Options menu. The hidden columns appear with a red cross.
-
Export Visible Columns as PDF: Use this option to export visible columns of the alert record to a
.pdffile.
Note: If you want to export records from the record's grid and view panel that contain unsupported character sets such as Korean or Chinese, then your administrators require to perform additional configurations. For more information, see the 'Configurations required for exporting of records with unsupported character sets in the PDF format' topic in the Debugging, Troubleshooting, and optimizing FortiSOAR chapter of the "Administration Guide." - Reset Columns To Default: Use this option to reset the alert record fields to the default fields specified for the alert module.
The following additional options are visible if you select the row(s) in the grid:
-
Export Selected Rows as CSV: Use this option to export selected rows in the alerts grid to a
.csvfile. -
Export Selected Rows as PDF: Use this option to export selected rows in the alerts grid to a
.pdffile.
Editing a record in the List view
Select a record in the list view to delete, clone, perform bulk and automated actions, on that record as shown in the following image:

To reassign a record to another user(s), select the record(s) and click the Reassign button. Clicking the Reassign button displays the Assigned To list. Select the user to whom you want to reassign the record(s) and click Reassign.
To delete a record, select the record and then click the Delete button.
|
|
Deleting a record deletes the data and the relationships to the record, but not the entities to which the record is related. |
To clone a record, select the record and then click the Clone button, which opens a Clone Records dialog. In the Clone Records dialog choose whether you want to clone only the record, or also the related records for that record; if you want to clone the related records also, select the Include Relationships checkbox and click Confirm. Once you clone a record, you can edit it as per your requirements. FortiSOAR names the cloned record as Copy of <content of the Name field>. In case the record does not have the Name field in its MMD, then FortiSOAR picks up the value of the first field that is of text format. For example, in the case of the Indicator module, Value is the first field that is of text format. So, if you clone an indicator record, the cloned record will be named as Copy of <content of the Value field>.
|
|
You can clone only up to 100 records in a single selection. Select 100 records or less to perform the clone operation. |
Executing default actions on records in bulk
If your administrator has configured bulk edit on a field in a particular module, then you can modify those records in bulk. The Change Email Classification (introduced in 7.2.0), Reassign, Change Severity, Change Status, Change Queue (introduced in 7.2.0), Execute, Escalate, and Resolve buttons are bulk operation buttons, which are included by default in FortiSOAR. For example, you can update the email classification of records to Phishing or Non Phishing, by selecting the records and clicking Change Email Classification, and then selecting Phishing or Non Phishing. Or, you can change the queue to which the records are assigned by selecting the records and clicking Change Queue and then selecting the queue to which you want to assign the records.
Your administrator can also configure the bulk edit operation on any other field, such as Type, in the Alerts module, then you can select multiple records and perform a bulk change on that field. Administrators can refer to the Application Editor chapter in the "Administration Guide" for the process of configuring Bulk Edit.
Example of the working of Change Severity: In case of Change Severity, you can select multiple records and change their Severity to the same particular severity level. Select multiple records and click the Change Severity button, which displays a Severity dialog box. The Severity dialog box contains the severity options configured, for example, Critical, High, Medium, etc. Select the severity level that you want to set for the multiple records, for example, select High.

Once you click the severity that you want to set for the records, you will see a Success message, and see that the Severity level of the selected records has all been modified to High, as shown in the following image:

You can also change the status of multiple records to the same particular status level in the same way and also perform a bulk reassign to records to a particular person. You can also close multiple records in bulk by selecting multiple records and then clicking the Resolve button. Once you click the Resolve button FortiSOAR displays a Resolve dialog in which you are required to add the reason for closing the alerts in the Closing Reason field and click the Execute button. This reason that you add for closing the alert is included in the Closure Notes fields, and the status of the records is changed to Closed.
Example of escalating an alert to an incident: When your administrator is editing the template for a module, the administrator can create buttons for commonly used actions on that module. For more information on editing templates, see the Dashboard, Templates, and Widgets chapter. For example, the Escalate button for the Escalate manual trigger on the Alerts module, which escalates alerts to incidents is included by default in FortiSOAR.
You can select an alert record or records in the grid view and click the Escalate button to create a new incident based on the provided inputs and link the alert to the newly created incident.

For example, if you want to escalate a Critical alert to an incident, you must select that record from the grid and then click the Escalate button. This triggers the Escalate playbook and based on the configuration of this playbook; you must specify the value of specific fields, such specifying the name and severity (default set to "Medium") of the incident that will be created by the playbook, the person to whom this incident will be assigned, and the reason for escalation (default set to "Alert needs to be investigated.").

Click Escalate to run the playbook and based on whether the playbook runs successfully or not, you will get an appropriate message, success in our example, as shown in the following image:

You will see Yes in the Escalated column in the row of the alert that you have escalated. You can see that an incident is created based on your inputs by either clicking the Go to result link as shown in the previous image or by opening the Incidents module. In our example, we named the incident as Escalating a Critical Alert to an Incident, and the following image displays this newly created incident:

Executing playbook actions on a record
If you have registered any manual triggers on the module, in this case, the Alerts module, and you select a record, then you can see those actions listed in the Execute drop-down list. If you want to run any action against the selected record, then click Execute and select the action that you want to execute.

The names that are displayed in the Execute drop-down list are the names that you have specified as the playbook name or the name that you have specified in the Trigger Label Button field in a manual trigger playbook. If you have specified both, then the name you have specified in the in the Trigger Label Button field will be displayed in the Execute drop-down list. For more information about playbooks and triggers, see the Triggers & Steps chapter in the "Playbooks Guide."
For example, if you want to investigate a repeated login failure then select the alert for which you want to run the investigation and click the Investigate Brute Force option from the Execute drop-down list. This will run the Investigate Brute Force playbook as shown in the following image:

Important: FortiSOAR implements RBAC for playbooks, including the ability to define the ownership, Public or Private, for playbooks. A "Private" playbook is one that can be executed only by those teams to which it is assigned. A "Public" playbook is one that can be executed by all (if they have other appropriate rights). Execute actions include actions such as Escalate, Resolve, or any actions that appear in the Execute drop-down list on module records are shown based on ownership. For example, if you have created a Private playbook with a Manual Trigger on the Alerts module, and if you go to the alerts module and select the record, then the Execute drop-down list will contain only those playbooks that belong to your team(s). Also, you can only execute playbooks, if your administrator has assigned you a role that has the Execute permission selected for the Playbooks module.
Using Row Expansion in Grids
Administrators can also configure your template to display the overview for records, such as incident or alert records, without having to open that record in the detail view. For more information on how to configure the template, see the Dashboards, Templates, and Widgets chapter. If the template is configured for grid expansion, then you can click expand icon (>) in the record row to display the details for that record. The fields that are displayed here is dependent on what your administrator has configured in the template.
The following image illustrates how FortiSOAR displays the detail view of an alert whose template has been configured for grid expansion:

Alert Details View
When you click an alert in the list view, it opens the alert in the Detail view. You can view in-depth information about the alert as well as review comment activity and any records related to the alert (attachments, tasks, etc.). The details of the alert such as Severity, ID, Name, and the DateTime when the alert was last modified. You can also add or view tags associated with the record in the detail view. You can click icons that appear on the top right of the detail view to perform various actions:
- Click the Executed Playbook Logs icon (
 ) to view the logs and results of playbooks that have been executed on that alert record in the flowchart format. You can toggle between Current Record and All. The 'Current Record' view displays only the logs of the playbooks that are executed on that particular record whereas, the 'All' view displays logs for all the playbooks that are executed on the FortiSOAR system.
) to view the logs and results of playbooks that have been executed on that alert record in the flowchart format. You can toggle between Current Record and All. The 'Current Record' view displays only the logs of the playbooks that are executed on that particular record whereas, the 'All' view displays logs for all the playbooks that are executed on the FortiSOAR system. 
You can also purge Executed Playbook Logs for a particular alert by clicking the Settings icon on the top-right of theExecuted Playbook Logsdialog in the Detail view of that alert, and then selecting the Purge Logs option, which displays thePurge Playbook Execution Logsdialog. In thePurge Playbook Execution Logsdialog, select the time frame (using the calendar widget) before which you want to clear all the executed playbook logs. For more information on all the Executed Playbook Logs, see the Debugging and Optimizing Playbooks chapter in the "Playbooks Guide." - Click the Edit Template icon to design the detail view using templates. For more information on templates, see the Dashboards, Templates, and Widgets chapter.
- Click the Copy Record Link icon (
 ) to copy the record link to the clipboard and share the record. The record link gets copied to the clipboard as follows:
) to copy the record link to the clipboard and share the record. The record link gets copied to the clipboard as follows: https://{*Your_FortiSOAR_IP*} /modules/{*module_name*} /{*record_ID*}. For example,https://xx.xx.xx.xxx/modules/alerts/5f213267-8683-43c4-8560-b45eda413145.
The Details view by default has the following tabs:
- The Alert Details tab displays details of the alert such as to whom the alert is assigned, the status, severity, type, source, etc of the alert. The Alerts Details tab contains the following tabs:
- The Indicators tab displays the indicators such as URLs and IP addresses, which are linked to that alert record.
- The Correlations tab displays subtabs that display the entities to which the alert is actively related.
- The Tasks tab displays the tasks that are linked to that alert record.
- The Source Data tab displays the raw data of that alert record.
- The External Communications tab displays any external communication associated with that alert record.
- The Access Control tab displays the owners of that alert record.

- The Playbooks tab displays the logs and results of playbooks that have been executed on that alert in the flowchart format, as is displayed in the Executed Playbook Logs. This makes it easier for users to view the flow of playbooks, especially useful for viewing the parallel execution paths in playbooks. The same view can be seen when you click the Executed Playbook Logs icon on the top right of the Detail view.
For more information on all the Executed Playbook Logs and the details of the playbooks tab, see the Debugging and Optimizing Playbooks chapter in the "Playbooks Guide."
- The Audit Log tab displays the historical timeline, in a graphical format, for the current record. Click the Full-screen Mode button to view the audit log in the full-screen mode. You can expand and collapse the entries in the timeline (audit log) to view the details of the changes. For more information on
Timeline, see the Dashboards, Templates, and Widgets chapter.
Editing a record in the Alert Details tab
Overview
To edit the template for any module, including Alerts, click the Edit Template button. For more information on Templates, see the Dashboards, Templates, and Widgets chapter.
You can run actions on the record, such as escalating an alert to an incident by clicking the Escalate button. Or, you can resolve an alert by clicking the Resolve button. The Escalate and Resolve buttons have been explained in the Alerts List View section.
Click the Delete Record button to delete the alert record from the Details page.
|
|
Deleting an alert record deletes the alert data and the relationships to the record, but not the entities to which the alert is related. |
You can export the detailed information of the alert in the .csv and .pdf formats, by clicking the Export Record button.
|
|
If you want to export records from the record's grid and view panel that contain unsupported character sets such as Korean or Chinese, then your administrators require to perform additional configurations. For more information, see the 'Configurations required for exporting of records with unsupported character sets in the PDF format' topic in the Debugging, Troubleshooting, and optimizing FortiSOAR chapter of the "Administration Guide." |
From version 6.4.0 onwards, you can view fields related to SLA management in you alert or incident records. You will see fields such as Ack Due Date, Ack Date, Ack SLA, Response Due Date, etc. using which you can track whether or not the SLAs have been met. For more information, see the SLA Management chapter in the "Administration Guide."
You can execute a playbook on the record by clicking the Execute button and selecting the playbook that you want to run on the record. From version 6.4.0 onwards, you can also search through the list of playbooks by typing the search keywords in Search Playbook.

Click the Workspace icon (![]() ) to view the Workspace panel, which appears on the right side of the Detail view of a record and consists of the Comments tab and the Recommendations tab. You can use the Comments tab of the Workspace to add comments and attachments to the record. The Recommendations tab of the Workspace provides you with a list of similar records.
) to view the Workspace panel, which appears on the right side of the Detail view of a record and consists of the Comments tab and the Recommendations tab. You can use the Comments tab of the Workspace to add comments and attachments to the record. The Recommendations tab of the Workspace provides you with a list of similar records.
In the Comments tab, you can add comments and attachments to the record. Use the "Styling" toolbar to apply some formatting, such as bold, italics, underline, and strikethrough to the content that you add as a comment. From version 6.4.3 onwards, you can edit the Contents field in the "Comments" module, and choose how this field should be rendered, either Rich Text (Markdown), which is the default or as Rich Text (HTML).
The following image illustrates how the Comments widget is displayed in the Detail View of a record, when the "Content" field is set as Rich Text (HTML):

The following image illustrates how the Comments widget is displayed in the Detail View of a record, when the "Content" field is retained as Rich Text (Markdown):

You can mark a comment as important, by clicking the Mark Comment as Important icon. You can search for comments and also filter comments based on tags, mentions, and the importance flag.
From version 7.0.0 onwards, you can add mentions or tag users in comments. Typing @ in the comments displays the list of active users, with their first and last names highlighted in blue. Select the user who you want to tag from the list, which results in the IRI of the user being linked to that comment. Users who are tagged get notified of their mentions by email.

Message Threads or Nested Replies are introduced in comments to help in keeping track of conversations and making it easier to respond to a specific thread. Now, when users reply to a comment, the reply will be displayed as an indented (only a single level indent) comment. which helps in clear identification of replies to a comment and a new comment thread as seen in the above image. The first comment contains a message thread whose entire conversation you can view by clicking Show all <number of replies> replies. You can reply to the conversation by clicking Reply.
If you have large files or images to be added to comments, you can add them as attachments to the comments. Add files or images by dragging-and-dropping files or images (these are added as inline images) onto the comments panel, or by clicking the Attachments button. You can attach a maximum of five files to a single comment. Both Inline images and images that are attached get appropriately resized within comments. To view the images as per its original size so that it becomes possible to read the contents of the images, click the attachment name to see the enlarged image. In case of inline images, clicking the image name downloads the original image.
You can preview the comment by clicking on the Preview tab and click the Full Screen icon to make the workspace cover the complete screen. Press Enter or click the Post Comment icon to add the comment to the collaboration panel. Press Shift + Enter to add a new line.
You can increase the width of the workspace panel by clicking the Expand icon (![]() ). The Comments panel displays the latest 30 comments, and if you want to view older comments, then click the View More link that at the top of the Comments panel.
). The Comments panel displays the latest 30 comments, and if you want to view older comments, then click the View More link that at the top of the Comments panel.
You can edit and delete your own comments if your administrator has enabled the settings for comment modification and if you have appropriate CRUD permissions on the Comments module. You can edit or delete your comments within the time duration that your administrator has set, by default this is set to "5 minutes". This means that you can edit and delete your comments within 5 minutes of adding the comment.
If you want to edit a comment, click the Edit icon within the comment, make the necessary modifications to the comment and press Enter. The Collaboration Panel would now display the modified comment with the Modified <time when the comment was modified>, for example, Modified less than a minute ago, content appearing under the modified comment, as shown in the following image:

If you want to delete a comment, click the Delete icon within the comment and in the Confirmation dialog, click Confirm. Then Collaboration Panel would display the comment as - Comment Deleted - under the username, as shown in the following image:

You will observe the same behavior in case the Comments widget has been added in the detail view of the record.
Related records permissions are defined by the parent record, and therefore comments are associated with the record instead of the module. Therefore, anybody who can see the record as per ownership or team hierarchy can see all the comments added to that record irrespective of who added the comments to that particular record.
From version 6.4.0 onwards, the table view has been enhanced to allow for editing a table in the Collaboration Panel by clicking the Edit icon and also for viewing the table in the full screen by clicking the Full-Screen icon as shown in the following image:

Clicking the Full-Screen icon opens the table in the full screen as shown in the following image:

This enhancement makes it easier for you to view and edit large tables in the Collaboration Panel, especially those that have been converted from JSON to HTML using the "Util: Convert JSON into an HTML Table" action of the "Utilities" connector and added into the alert using a playbook as shown in the above image. In the full-screen mode also you can edit the table and you can export the table in the .csv format by clicking the Export Table as CSV link. Also, if there are more than "5" rows in the table then a Show More link will be displayed, clicking which you can view all the rows of the table.
Editing Records
Editing the complete record
To edit the complete record, click the Edit Record button, which opens the Edit Alert dialog that contains the details of the alert in a form. You can edit multiple fields at one time for the record and then click Save to save the changes to the record.

Editing Fields
To edit any fields in the record, go to that field, and if that field is an editable field then you can click and change the value of that field either by typing content in the text field or by selecting a value from a drop-down list.
The alerts detail view contains a Description field that provides the description of the alert and it is generally a "Rich Text" field. Rich Text fields allow you to apply formatting to the content entered in this field. Rich Text fields can either have a "Markdown" editor or an "HTML WYSIWYG" editor, based on the sub-type that is set for this text field. The default editor is set as "Markdown" for all modules, which can be changed to the "HTML" editor using 'Module Editor'.
You can add styles such as headings, bold, italics, add lists, tables, and insert links, images, attachments etc. using the "Styling" toolbar provided in the rich text field in both the Markdown and HTML editors. Note that video is not supported in the "Markdown" editor.
In case of the Markdown editor, you can write in markdown in the "Write" mode and click Preview to view how your content will be displayed. The following image displays content in the "Write" mode:

The following image displays content in the "Preview" mode:

You can also add an inline css or add inline styles such as "style="color:blue;"" to your content in the Rich Text field.
|
|
Some tags such as script, iFrame, textarea, form, select, meta, style, link, title, embed, object, details, and summary and some attributes such as onLoad are not supported in the Rich Text (Markdown) field and the Richtext Content widget. If you want to use these tags or attributes, contact FortiSOAR support. |
The following image displays editing of content of a rich text field using the HTML editor:

If the editor of the "Rich Text" field is changed from Markdown to HTML or vice-versa, note the following:
- If the content was in the HTML format and you change the format to Markdown, then the Markdown editor will display the HTML code in ''Write'' mode and the "Preview" will work fine.
- If the content was in Markdown format and you change the format to HTML, then the HTML editor will show the Markdown code in the source code mode; however, the content will not get rendered. You must convert the markdown code to HTML code for the content to correctly render the content.
Editing picklists or lookups
To change a value of a picklist or a lookup, select the required value from their respective drop-down list as shown in the following image:

|
|
By default, |
The lookup fields for the People module, such as Assigned To or Incident Lead, also contains a View button. Clicking the View button opens the User Profile page for that user.
FortiSOAR also supports a special type of picklist, called "Multiselect Picklist". You can use the multiselect picklist for fields that can contain more than one value. For example, you can have an alert be assigned more than one "Type", i.e., an alert can be of type Brute Force Alert and Malware. If your administrator has assigned "Multiselect Picklist" field type to any picklist, then you can assign more than one value to that field as shown in the following image:

Working with Related Records
Clicking the Correlations tab displays subtabs that contain the entities, such as incidents or emails or events, to which the alert is actively related.

Clicking the < icon collapses the subtabs and displays entities to which the alert has an active relationship and clicking > icon expands the subtabs displaying all the entities.
If you want to add relationships to any other entity, click that entity and then click the Link {Entity} button. For example, to link an incident to an alert click Incidents and then click the Link Incidents button. This displays the Change Relationship dialog which displays the list of Incidents. Click the incident that you want to link to the alert and then click Save Relationship to add the incident as a related record to the alert.

You can perform update field operations on the related item, such as change status, change severity and change lead, by clicking the respective buttons. The operation of these fields is similar to Executing default actions on records in bulk. To remove a relationship, select the related item and click Remove Link.

Related records permissions are defined by the parent record. For example, if there is an alert record that contains a related incident record to which you do not have permissions, you will be able to view that incident record (read-only permissions) in the Related Records tab.
You can also view the relationships of a particular record in a graphical format, by adding the Visual Correlation widget to the detail view of the records. For more information, see the Dashboards, Templates, and Widgets chapter.
Viewing Breadcrumbs
FortiSOAR displays breadcrumbs in the top bar of a record so that you can view your navigational trail and immediately know your location within FortiSOAR. Using the breadcrumbs, you can navigate easily through several related records and come back to your original record.
For example, click a record in a module, for example, Alerts, then click the Related Records tab, click the Incidents subtab, select the related incident. You will see the breadcrumbs in the top bar of the record, as shown in the following image:

Using Grid Expansion in Relationships
If your administrator has configured your template to display the overview of related records in the detail view of the record itself without having to open the related record in a new window. For example, you can view the details of an incident related to an alert in the alert detail view itself, without having to open the incident record in a new window. For more information on how to configure the template, see the Dashboards, Templates, and Widgets chapter. If the template is configured for grid expansion, then you can click expand icon (>) in the related record row to display the details for that record. The fields that are displayed here is dependent on what your administrator has configured in the template.
The following image illustrates how FortiSOAR displays the detail view of an alert and its Related Records tab, with the Incidents tab selected. The Incidents records have been configured for grid expansion:

Applying different default filters for each relationship grid
You can apply different default filters for each relationship grid widget. For example, if in the alert details, you want one relationship grid to display only "Suspicious" Indicators and another to display only "Malicious" Indicators, this can be achieved as follows:
- In the alerts detail view, add a relationship grid for Indicators, named "Suspicious Indicators" as follows:
- Open an alert in the detail view and click Edit Template.
- In the Template Editing Mode, go towards the end of the template, where various tabs for related records are present, and click New Tab, and enter the title as
Suspicious Indicatorsand click the green checkbox.
Then, click Add Widget in the Suspicious Indicators tab and optionally add an icon for this tab. rom theChoose Widgetdialog, select Relationships. Click Edit in the Relationships grid, and in theRelationshipsdialog, click Remove All and then from the Select a module drop-down list, select Indicators, click Add To View and click Save.
This creates a tab called Suspicious Indicators in theRelated Recordssection in the alert details page.
Similarly, perform the above steps for creating the Malicious Indicators tab.
- In the Suspicious Indicators tab, create a filter for "Reputation = Suspicious" as follows:
- Click Filters and from the Reputation drop-down list select Suspicious and click Apply.
This creates a filter as shown in the following image:

- Click the Save Filter drop-down list as select the Save as System option (if you want this filter to be applicable to all users) which opens the
Save As System Filterdialog, in which enter the name of the filter such as,Reputation is Suspicious, and click Save. - Click the star icon to save this filter as the default filter to be applied to this gird and click Save Filter.

- Perform steps similar to the above steps for creating the
Reputation is Maliciousfilter.
- Click Filters and from the Reputation drop-down list select Suspicious and click Apply.
This creates a filter as shown in the following image:
Once you have added these default filters, you will observe that the relationship grid in the Suspicious Indicators tab will contain only those indicators whose reputation is suspicious.

Similarly, you will observe that the relationship grid in the Malicious Indicators tab will contain only those indicators whose reputation is malicious.

Invoking connector actions directly on a record
You can invoke connector actions directly in the detail view of a record and investigate the alert without the need of writing a playbook.
|
|
To run connector actions on the record, you must be assigned a role that contains |
For example, if want to retrieve the reputation of a source IP address in an alert from a threat intelligence tool such as VirusTotal, you can do the following:
- Open the detail view of the alert record on which you want to run the connector action.
- Click the Actions button.
You will see the Actions button, if the Show Action Execution Panel checkbox is selected, which is the default option. For more information, see the Dashboard, Template, and Widgets chapter.
Note: The Actions list only displays the active and installed connectors. - Search for actions that you want to perform using the Search Action box. For example, if you want to search for a reputation of an IP address, then you can type
IPin the Search Action box, and the connectors that have any action related to an IP address will be displayed:
As shown in the above image, VirusTotal, IBM XForce, URL Scan.io, etc connectors have "IP" in their actions. Click the down arrow to view the actions associated with IP for each connector. For example, if you click VirusTotal, you will see the "Get IP Reputation" action:
You can also clear the filter and view all the actions associated with a connector by clicking the connector and viewing its actions:
- Click the action that you want to perform on the alert. For our example, click Get IP Reputation (associated with VirusTotal), which displays the VirusTotal dialog. From version 6.4.1 onwards, you are required to specify whether you want to run the direct connector action on the current FortiSOAR node or remotely on the FSR agent node by clicking the Self or Agent buttons besides
Target. By default, Self is selected, which means that the connector action will run on the current FortiSOAR node, then you must select the configuration using which you want to run the connector action since the FortiSOAR node can have multiple configurations. If you click Agent, then you can select the FSR agent on which you want to run the connector action and you must also select the configuration using which you want to run the connector action since FSR agents can have multiple configurations. For more information on FSR agents and how to run direct connector actions using FSR agents, see the Segmented Network support in FortiSOAR chapter in the "Administration Guide." For our example, we have chosen Self.
Next, in the Input tab, in the IP field, either enter an IP address or use the value of a record field. For our example, we will use the value of the IP address that is present in the Source IP field. To input the value from a record field, in theInputtab, click the IP field, which displays anExpression Builderdialog. On the Record Fields tab, select or search for the record field, using the Search Fields box, that you want to add as the input to the connector action. For our example, select Source IP:
From the Relationships to Include list, you can also select the relationships such as Comments, Graphs, etc that you want to include in the output. - To run the connector action, click Execute Action.

- Once the connector action is executed, you can see the formatted output of the action, in a tabular format, as shown in the following image:

You can also view the output and in the JSON format:
You can also copy the output to the clipboard.
Select the output keys that you want to save, for example attributes. You can also add tags such asEvidenceto the results making it easy for you to search for and filter the outputs. For example, you can add a tagipRepFromVTto mark that the reputation of the specified IP address is got from VirusTotal, and also mark this action log as 'Evidence' by adding theEvidencetag, and then click Save selected output keys.
The output keys get saved as Action Log in the Comments tab in the Workspace section:
Also, since we also added a tag to the output, you can see the ipRepFromVT and Evidence tags added to the entry in the Comments tab.
When you click View Details, you can see the output that has been saved:
You can also consume the saved output for past connector actions as an input to another connector action within the record. For example, you want to get the reputation of a filehash using the Anomali ThreatStream connector, which supports only the MD5 as a filehash value and you have only the SHA256 value. In this case, you can extract and save the MD5 value from a filehash using the Get File Reputation action in VirusTotal:

Then, you can use the saved MD5 value to get the reputation of this filehash from Anomali ThreatStream, by clicking the Actions button and selecting the Get File Reputation action from the Anomali ThreatStream. In the Input tab, click the Filehash field, which displays the Expression Builder. Click the Past Action Outputs tab, where you can view the saved output of the past 10 actions. Select the action whose output you want to consume, in our example, choose the Get File Reputation action (from VirusTotal) and select or search for the parameter ("md5") that you add to the field:

To run the action on the record and retrieve the reputation of the MD5 filehash from Anomali ThreatStream, click Execute Action:

You can then check the output of the connector action and further perform actions as described earlier, including adding output keys to the action log and adding tags for future processing.
Using record similarity
FortiSOAR displays records that are similar to the record on which you are working. For example, FortiSOAR will display alerts that contain similar file hashes, source IP, domains, etc. based on the similarity criteria you have defined.
A scenario where analysts can use this feature would be the case of a Phishing alert being created in FortiSOAR from your Email Gateway. Users might click the URLs which in turn will create multiple Malware alerts from your SIEM (or Endpoint Detection Response tools). Therefore, a single event, i.e., a Phishing email generates alerts of different types (Malware, Policy Violation, Suspicious Email, etc) in FortiSOAR. Since FortiSOAR displays similar alerts to the alert an analyst is working on, it provides the analyst the complete picture of the event and makes it easier for the analyst to take remedial action.
|
|
The Recommendation Panel can be enabled and configured with default criteria if the Enable Recommendation Panel checkbox is checked in the template of a module. For more information, see the Dashboards, Templates, and Widgets chapter |
|
|
From version 7.0.0 onwards, two strategies are supported by FortiSOAR: Elasticsearch Based Text Classification (default) and Machine Learning Based Clustering for the similarity feature. For more information on these strategies, see the 'Recommendation Engine' topic in the Application Editor chapter in the "Administration Guide." |
Administrators define the similarity criteria based on which the Recommendation pane displays similar alerts. For example, administrators can define similarity criteria is based on the source and indicators of the alert. Therefore, alerts whose source or indicators, such as domains, IP addresses, URLs, etc., match the source or indicators of the alert record on which you are working get displayed in the Similar Records list:

As seen in the image above, the alerts that match the "Indicator" criteria (which are gumblar.cn, http://ghari.pk, etc.) are displayed first and then the alerts that match the "Source" criteria (which is IMAP), since the settings are such that the indicator criteria have been given greater weight than the source criteria.
The Playbooks drop-down list displays the list of playbooks that you had specified while configuring the recommendation settings. In our example, we had selected the Indicator Evaluation playbook, which gets displayed in the Playbooks drop-down list. You can select a similar record or click Select All to select all the similar records, and then click Indicator Evaluation to execute the playbook on that record(s). To execute the Indicator Evaluation playbook on the current (parent) record also, i.e., Alert 15... in the above image, select Include this record checkbox. Therefore, you can choose to execute the selected playbook on the current record as well as the selected similar record(s).
You might also want to perform an action, for example, Resolve, on similar alerts (records) but you do not want to resolve the current (parent) record, i.e., Alert 15.... However, you do want to link the similar records to the parent record, then in the Resolve Alert playbook, which is present in Playbooks > 08 - Escalation playbook collection, open the "Update Record" step and in the Alerts field (under Correlations section), enter vars.request.data.__parentId. This is also useful if you want to resolve duplicate records and keep only the parent record open.
Predicting values of field values in a record
FortiSOAR predicts values of fields of your choice within a record from the values of fields of existing records based on the criteria you have defined, making it easier for analysts to make informed decisions.
A scenario where analysts can use this feature would be the case of an alert, where you want FortiSOAR to predict the severity and assign the alert to a particular user, based on matching the alert's indicators and type.
|
|
From version 7.0.0 onwards, two recommendation strategies are supported by FortiSOAR: Elasticsearch Based Text Classification (default) and Machine Learning Based Clustering. For more information on these strategies, see the 'Recommendation Engine' topic in the Application Editor chapter in the "Administration Guide." |
Administrators define the field suggestions criteria based on which the Recommendation pane displays suggestions for field values. For example, administrators can define that the Severity and Assigned To fields can be predicted from the Type and Indicators fields. Based on the prediction criteria that has been defined, the Recommendation pane can display field value suggestions as follows:

As shown in the above image, FortiSOAR recommends that the severity of the record should be set to "Medium" and the record be assigned to "T1 Analyst". FortiSOAR makes these predictions based on the criteria that the administrators have set, and the ranking that is given to matching records.
If you agree to the suggestions and want to make the change in the record, click the green checkbox in the row of the field, which in turn will update or add the field value in the record. For example, if you want to update the value of the severity of the record to match the suggested similarity, then click the green checkbox in the severity row:

As shown in the above image, once you click the green checkbox, the value of the severity field changes from Low to Medium as per the predicted field value.
Similarly, you can also add T1 Analyst in the Assigned To field:

Viewing Suggestions for Phishing Classifications
From release 7.2.0 onwards, if your administrator has set up the 'Phishing Classification' feature, then in the Recommendation tab of the Workspace panel, you can also see suggestions on whether or not an alert record can be classified as a 'Phishing' record as shown in the following image:
You will see a Suggestion section with contains the Is this Phishing? question followed by the answer to that question and the corresponding confidence level. For example, in the above image, the answer to the Is this Phishing? question is Yes, with 99% confidence that it is a phishing email (record). You will also see that the Email Classification drop-down list has been set to 'Phishing'. Using this suggestion and its corresponding confidence value it becomes easy for you to classify records into 'Phishing' and 'Non Phishing' and accordingly proceed with the investigation process.
|
|
If you have installed and configured the Phishing Classifier connector on an agent node, and not on the FortiSOAR (base) node, then suggestions are not displayed in the Recommendations tab on the |

