CyberArk Password Vault
Using CyberArk as a Credential Vault with FortiSIEM
The CyberArk Vault can be utilized by FortiSIEM to securely access and retrieve usernames and passwords for authentication against devices and applications. To use this feature, both CyberArk and FortiSIEM must be configured.
Configuring CyberArk
There are two methods to integrate CyberArk with FortiSIEM, using the REST API (CCP) or Java SDK. FortiSIEM supports both methods, however the preferred method is the REST API. The following steps provide instructions for configuration through the REST API.
After logging into CyberArk, take the following steps:
-
Go to the Applications section.
-
Create a new application and in the Name field, enter a name.
or
Select an existing application. -
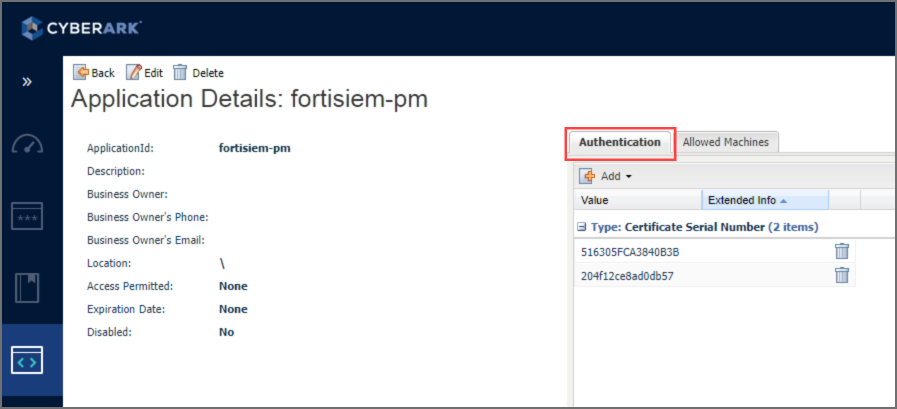
Select the Authentication tab.
-
Create certificates, and download the following:
Note: FortiSIEM requires the use of certificates as part of the authentication.-
Root CA
-
SSL Certificate
-
SSL Key File
-
-
Ensure that the application has access to the Safe where the Credentials are stored.

If you need to associate the Credential with a Safe, take the following steps:
-
Navigate to Policy.
-
Locate the Safe.
-
Click Members.
-
Click Add Member.
-
Add the Application.
-
Ensure the Retrieve accounts checkbox is checked. If it isn't, enable it.

-
Configuring FortiSIEM
Complete these steps in the FortiSIEM UI:
-
Navigate to ADMIN > Setup and click the Credentials tab.
-
In Step 1: Enter Credentials:
-
Follow the instructions in “Setting Credentials“ in the User's Guide to create a new credential.
-
Enter these settings in the Access Method Definition dialog box and click Save:
Setting Value Name Enter the name of the credential. Device Type Define the device type. Access Protocol Define the access protocol. Password Config Select CyberArk Rest API. Endpoint Enter the DNS name or IP of the CyberArk server. The format should be https://<server>:<port> Root CA
Upload the Root CA from CyberArk.
SSL Certificate
Upload the SSL Certificate from CyberArk.
SSL Key File
Upload the SSL Key File from CyberArk.
App ID Provide the application defined in CyberArk. Safe
Provide the safe defined in CyberArk.
Folder
Provide the folder from the CyberArk configuration. If folders are not used, specify "root".
Object
Provide the credential Account Name from CyberArk. This can be found in CyberArk under Accounts > <your account> > Details > <Account Name>.
Note: See screenshot below for example Account Name.
If the Object is defined in the FortiSIEM credential, then the follow additional details should not be needed:-
Username
-
Platform (Policy ID)
-
Database
-
(Checkbox) Include Address for Query
If this information is required, it can be obtained by using the thick client CyberArk tool PrivateArk. Take the following steps:
-
Open PrivateArk.
-
Open the Vault.
-
Find the Safe you wish to use.
-
Locate the credential, right click and select Properties.
Here you will find the Username and Policy ID.
-
-


What is Discovered and Monitored
|
Protocol |
Information discovered |
Logs parsed |
Used for |
|---|---|---|---|
|
Syslog (CEF formatted and others) |
|
CyberArk Safe Activity |
Security Monitoring and compliance |
Event Types
In ADMIN > Device Support > Event Types, search for "CyberArk-Vault" to see the event types associated with this device.
Rules
In RESOURCES > Rules, search for "CyberArk" in the in the main content panel Search... field:
- CyberArk Vault Blocked Failure
- CyberArk Vault CPM Password Disables
- CyberArk Vault Excessive Failed PSM Connections
- CyberArk Vault Excessive Impersonations
- CyberArk Vault Excessive PSM Keystroke Logging Failure
- CyberArk Vault Excessive PSM Session Monitoring Failure
- CyberArk Vault Excessive Password Release Failure
- CyberArk Vault File Operation Failure
- CyberArk Vault Object Content Validation Failure
- CyberArk Vault Unauthorized User Stations
- CyberArk Vault User History Clear
Reports
In RESOURCES > Reports, search for "CyberArk" in the main content panel Search... field:
- CyberArk Blocked Operations
- CyberArk CPM Password Disables
- CyberArk CPM Password Retrieval
- CyberArk File Operation Failures
- CyberArk Impersonations
- CyberArk Object Content Validation Failures
- CyberArk PSM Monitoring Failures
- CyberArk Password Resets
- CyberArk Privileged Command Operations
- CyberArk Provider Password Retrieval
- CyberArk Trusted Network Area Updates
- CyberArk Unauthorized Stations
- CyberArk User History Clears
- CyberArk User/Group Modification Activity
- CyberArk Vault CPM Password Reconcilations
- CyberArk Vault CPM Password Verifications
- CyberArk Vault Configuration Changes
- CyberArk Vault Failed PSM connections
- CyberArk Vault Modification Activity
- CyberArk Vault PSM Keystore Logging Failures
- CyberArk Vault Password Changes from CPM
- CyberArk Vault Password Release Failures
- CyberArk Vault Successful PSM Connections
- Top CyberArk Event Types
- Top CyberArk Safes, Folders By Activity
- Top CyberArk Users By Activity
CyberArk Configuration for Sending syslog in a Specific Format
- Open \PrivateArk\Server\DBParm.ini file and edit the SYSLOG section:
- SyslogServerIP – Specify FortiSIEM supervisor, workers and collectors separated by commas.
- SyslogServerProtocol – Set to the default value of UDP.
- SyslogServerPort – Set to the default value of 514.
- SyslogMessageCodeFilter – Set to the default range 0-999.
- SyslogTranslatorFile – Set to Syslog\FortiSIEM.xsl.
- UseLegacySyslogFormat - Set to the default value of No.
- Copy the relevant XSL translator file here to the Syslog subfolder specified in the SyslogTranslatorFile parameter in DBParm.ini.
- Stop and Start Vault (Central Server Administration) for the changes to take effect.
Make sure the syslog format is as follows.
<5>1 2016-02-02T17:24:42Z SJCDVVWCARK01 CYBERARK: Product="Vault";Version="9.20.0000";MessageID="295";Message="Retrieve password";Issuer="Administrator";Station="10.10.110.11";File="Root\snmpCommunity";
Safe="TestPasswords";Reason="Test";Severity="Info"
<30>Mar 22 20:13:42 VA461_1022 CyberArk AIM[2453]: APPAP097I Connection to the Vault has been restored <27>Mar 22 20:10:50 VA461_1022 CyberArk AIM[2453]: APPAP289E Connection to the Vault has failed. Further attempts to connect to the Vault will be avoided for [1] minutes. <27>Mar 24 23:41:58 VA461_1022 CyberArk AIM[2453]: APPAU002E Provider [Prov_VA461_1022] has failed to fetch password with query [Safe=TestPutta;Object=Telnet91] for application [FortiSIEM]. Fetch reason: [APPAP004E Password object matching query

