Cisco pxGrid/ISE
A new fabric connector is added for Cisco pxGrid. When enabled, FortiManager centralizes the updates from pxGrid for all FortiGate devices, and leverages the efficient FSSO protocol to apply dynamic policy updates to FortiGate.
Deploying pxGrid connector consists of the following steps:
- Configure Cisco ISE Server.
- Configure FortiManager.
Configure Cisco ISE Server
To configure Cisco ISE server:
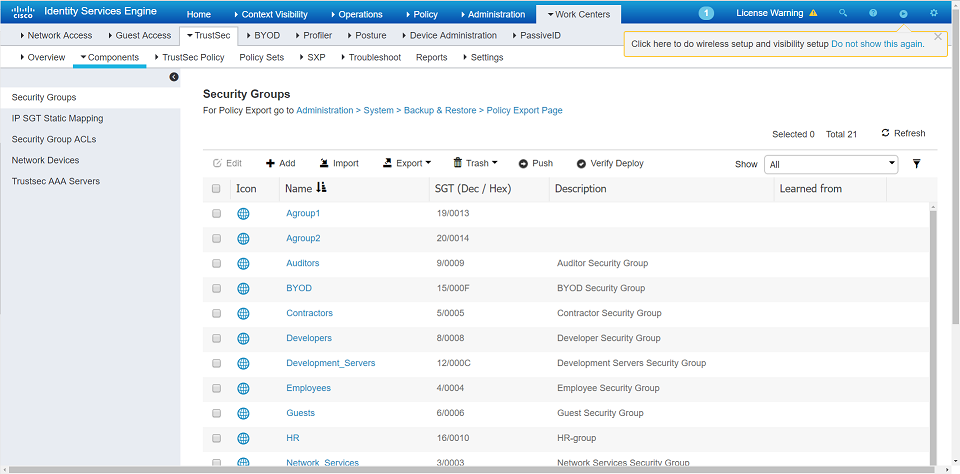
- Create a Security Group: Go to ISE > Work Centers > TrustSec > Components > Security Groups. Click Add.
- Create a User Identity Group: Go to ISE > Administration > Identity Management > Groups > User Identity Groups. Click Add.

- Create a user and add it to User Identity Group: Go to ISE > Administration > Identity Management > Identities. Click Add.

- Match the Security Group with User Identity Group in the policy: Go to ISE > Work Centers >TrustSec > Components > Policy Sets. Right-click and go to Authorization policy > Basic_Authenticatied _Access and click Edit to match the Security Group with the User Identity Group.

- Generate the pxGrid certificate and download it to the local computer: Go to ISE > Administration > pxGrid Services > Certificate and select Generate pxGrid Certificates.

- See log for current users: Go to ISE > Operations > RADIUS > Live Logs.

- See live sessions of current users: Go to ISE > Operations > RADIUS > Live Sessions.

Configure FortiManager
To configure FortiManager:
- Go to System Settings > Local Certificates > Import. Import the downloaded certificate.

- Go to Fabric View > Fabric Connectors. Create a new pxGrid Fabric Connector with the imported certificate.

- Go to Policy & Objects > Object Configuration > Single Sign-On. Select the connector and click Import.

- The pxGrid connector is imported. Click Close to close the import dialog.

- Click User Groups and create a new group. Set the type as FSSO/Cisco TrustSec, and select pxGrid user as a member.

- Create a policy with the ISEgroup user group and install the policy to FortiGate.

- Go to Fabric View > Fabric Connectors. Click Monitor to see the users currently logged in.

- Log on to FortiGate to view the ISE user group.

- On the FortiGate command line, use the
diagnose debug authd fssolist to monitor the current user list.
Command Line
Command line for FortiManager:
config system connector
set
fsso-refresh-interval FSSO refresh interval (60 - 1800 seconds).
fsso-sess-timeout FSSO session timeout (30 - 600 seconds).
px-refresh-interval pxGrid refresh interval (60 - 1800 seconds).
px-svr-timeout pxGrid server timeout (30 - 600 seconds).
Realtime monitor debug to watch server connection:
diag debug application connector 255
Command line for FortiGate:
diag debug authd fsso server-status
diag debug authd fsso list-------> show connected users
----FSSO logons----
IP: 192.168.1.19 User: test2 Groups: px_fc1_security_grp1 Workstation: MemberOf: fscs1
IP: 192.168.1.20 User: test2 Groups: px_fc1_security_grp1 Workstation: MemberOf: fscs1
Total number of logons listed: 2, filtered: 0
----end of FSSO logons----
diag debug authd fsso refresh-logon
diag debug authd fsso refresh-group

