Support TLS 1.3 for proxy forward servers in certificate inspection mode 6.4.1
The FortiGate web proxy forward server now supports TLS 1.3. Prior to 6.4.1, if the server requested TLS 1.3, the web proxy forward configuration was unable to accommodate it, so no hello retry request was sent back to the client and the connection was stuck in the client hello phase.
Example
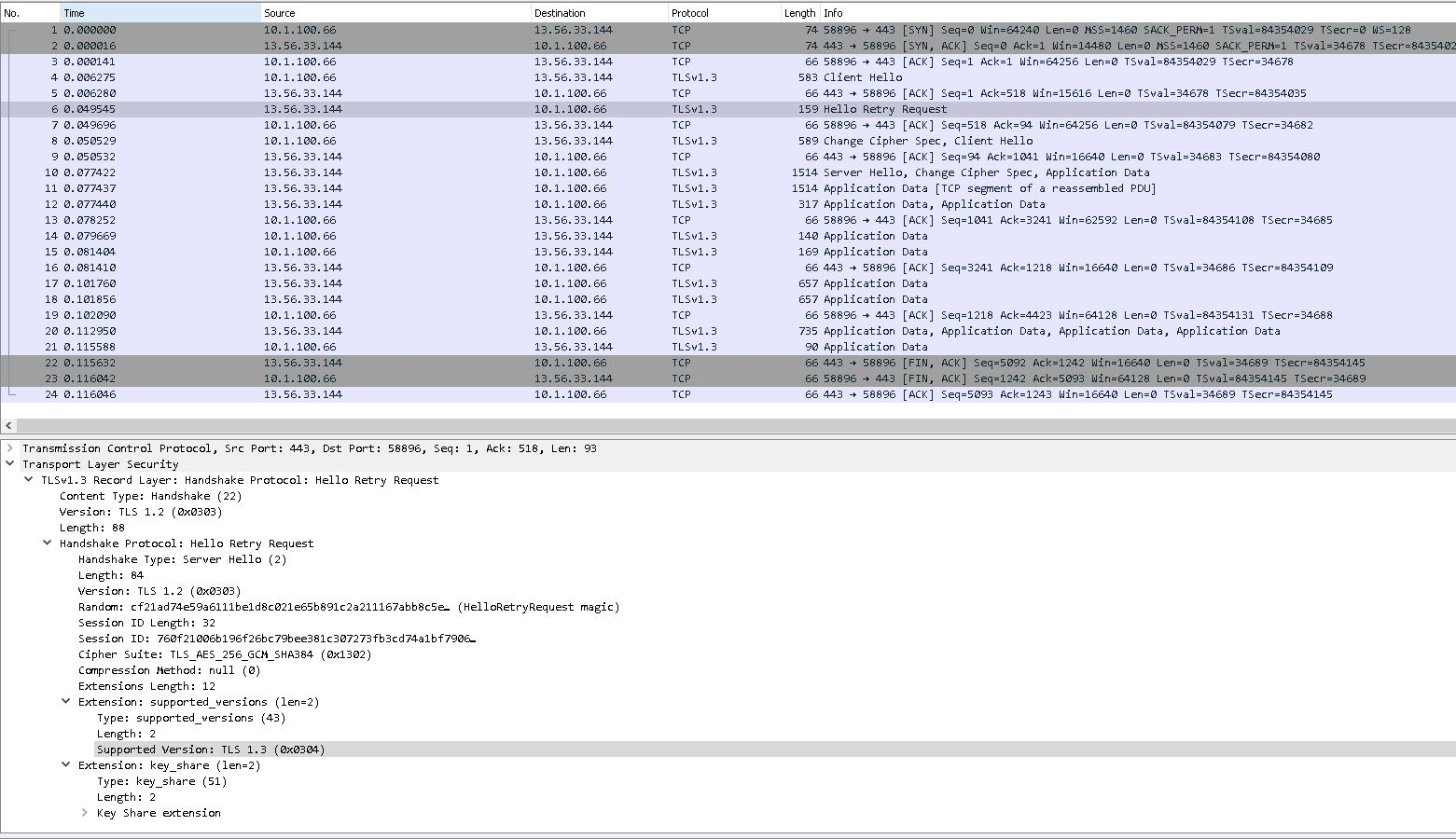
In the following example, the Squid server and the FortiGate can handle TLS 1.3 traffic in both deep and certificate inspection modes.

The following output from the Squid server demonstrates that the FortiGate supports TLS 1.3 traffic and forwards the hello retry request back to the client PC. The client PC then sends the client hello again, and the connection is successfully established.