Configure DSCP for IPsec tunnels 6.4.3
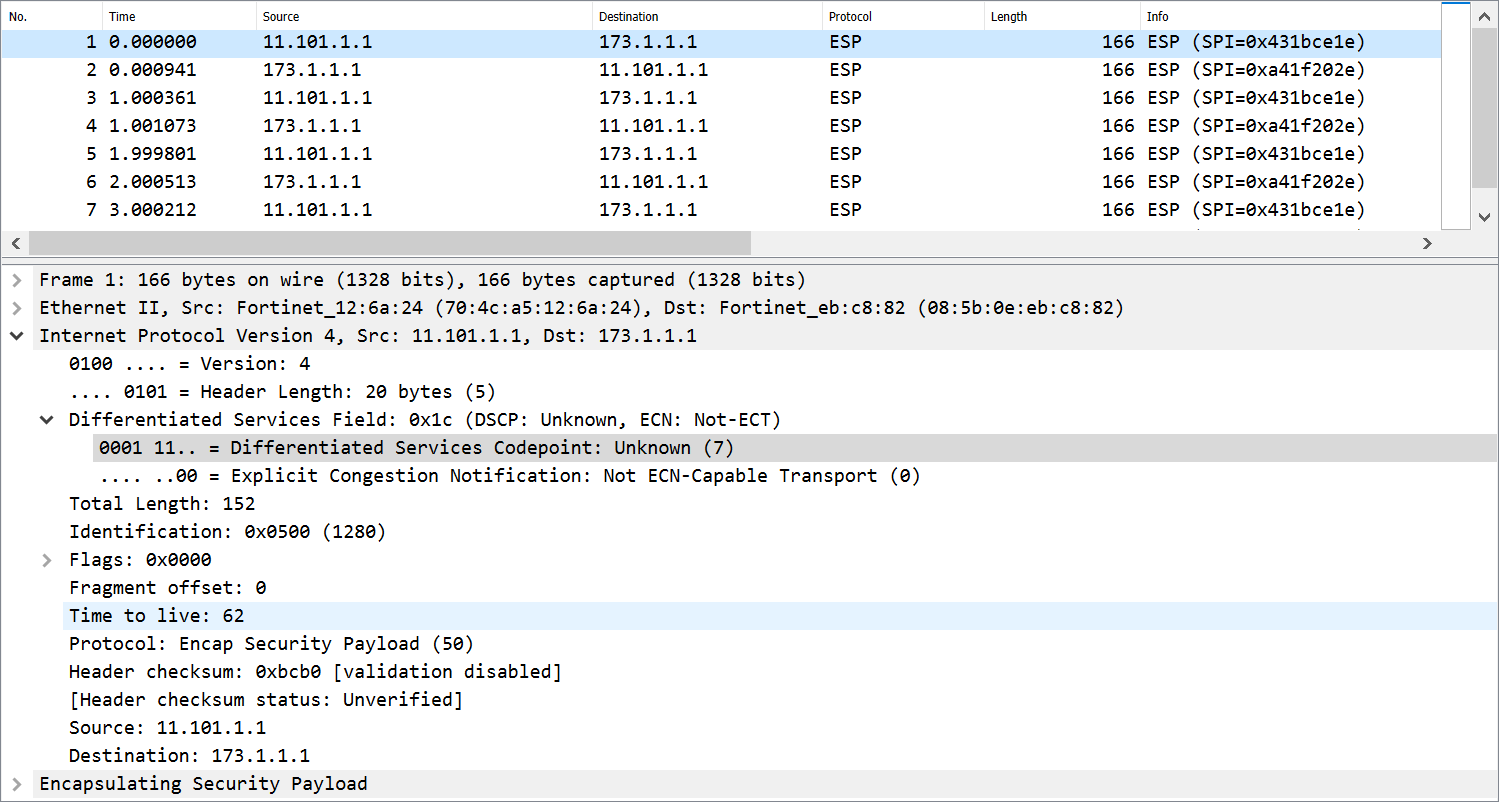
Configuring the differentiated services (DiffServ) code in phase2 of an IPsec tunnel allows the tag to be applied to the Encapsulating Security Payload (ESP) packet.
-
If
diffservis disabled in the IPsec phase2 configuration, then the ESP packets' DSCP value is copied from the inner IP packet DSCP. -
If
diffservis enabled in the IPsec phase2 configuration, then ESP packets' DSCP value is set to the configured value.
|
|
Offloading traffic to the NPU must be disabled for the tunnel. |

In this example, NPU offloading is disabled, diffserv is enabled, and the diffserv code is set to 000111 on FGT-A. Only one side of the tunnel needs to have diffserv enabled.
To configure IPsec on FGT-A:
-
Configure the phase1-interface:
config vpn ipsec phase1-interface edit "s2s" set interface "wan1" set peertype any set net-device disable set proposal aes128-sha256 aes256-sha256 aes128-sha1 aes256-sha1 set npu-offload disable set dhgrp 14 5 set wizard-type static-fortigate set remote-gw 173.1.1.1 set psksecret *********** next end -
Configure the phase2-interface:
config vpn ipsec phase2-interface edit "s2s" set phase1name "s2s" set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 set dhgrp 14 5 set diffserv enable set diffservcode 000111 set src-addr-type name set dst-addr-type name set src-name "s2s_local" set dst-name "s2s_remote" next end -
Check the state of the IPsec tunnel:
FGT-A # diagnose vpn tunnel list list all ipsec tunnel in vd 0 ------------------------------------------------------ name=s2s ver=1 serial=1 11.101.1.1:0->173.1.1.1:0 dst_mtu=1500 bound_if=17 lgwy=static/1 tun=intf/0 mode=auto/1 encap=none/512 options[0200]=frag-rfc run_state=0 accept_traffic=1 overlay_id=0 proxyid_num=1 child_num=0 refcnt=11 ilast=12 olast=2978 ad=/0 stat: rxp=4 txp=4 rxb=608 txb=336 dpd: mode=on-demand on=1 idle=20000ms retry=3 count=0 seqno=0 natt: mode=none draft=0 interval=0 remote_port=0 proxyid=s2s proto=0 sa=1 ref=2 serial=2 dscp src: 0:10.1.100.0/255.255.255.0:0 dst: 0:174.16.101.0/255.255.255.0:0 SA: ref=3 options=110226 type=00 soft=0 mtu=1438 expire=39916/0B replaywin=2048 seqno=5 esn=0 replaywin_lastseq=00000005 itn=0 qat=0 hash_search_len=1 life: type=01 bytes=0/0 timeout=42899/43200 dec: spi=a41f202e esp=aes key=16 8a02875b80b884d961af227fe8b5cdee ah=sha1 key=20 fc9760b79e79dbbeef630ec0c5dca74777976208 enc: spi=431bce1e esp=aes key=16 851117af24212da89e466d8bea9632bb ah=sha1 key=20 0807cc0af2dc4ea049a6b1a4af410ccc71e2156d dec:pkts/bytes=4/336, enc:pkts/bytes=4/608 npu_flag=00 npu_rgwy=173.1.1.1 npu_lgwy=11.101.1.1 npu_selid=1 dec_npuid=0 enc_npuid=0 run_tally=1 -
Use a packet analyzer, or sniffer, to check the ESP packets: