SSL VPN with FortiToken two-factor authentication
This is a sample configuration of SSL VPN that uses FortiToken two-factor authentication (2FA).
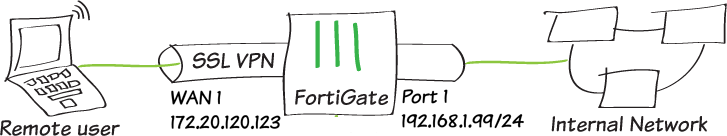
Sample topology
Sample configuration
WAN interface is the interface connected to ISP. This example shows static mode. You can also use DHCP or PPPoE mode. The SSL VPN connection is established over the WAN interface.
To configure SSL VPN using the GUI:
- Configure the interface and firewall address. The port1 interface connects to the internal network.
- Go to Network > Interfaces and edit the wan1 interface.
- Set IP/Network Mask to 172.20.120.123/255.255.255.0.
- Edit port1 interface and set IP/Network Mask to 192.168.1.99/255.255.255.0.
- Click OK.
- Go to Policy & Objects > Address and create an address for internal subnet 192.168.1.0.
- Register FortiGate for FortiCare Support.
To add or download a mobile token on FortiGate, FortiGate must be registered for FortiCare Support. If your FortiGate is registered, skip this step.
- Go to Dashboard > Licenses.
- Hover the pointer on FortiCare Support to check if FortiCare registered. If not, click it and select Register.
- Add FortiToken mobile to FortiGate.
If your FortiGate has FortiToken installed, skip this step.
- Go to User & Device > FortiTokens and click Create New.
- Select Mobile Token and type in Activation Code.
- Every FortiGate has two free mobile tokens. Go to User & Device > FortiTokens and click Import Free Trial Tokens.
- Configure user and user group.
- Go to User & Device > User Definition to create a local user sslvpnuser1.
- Enter the user's Email Address.
- Enable Two-factor Authentication and select one mobile Token from the list,
- Enable Send Activation Code and select Email.
- Click Next and click Submit.
- Go to User & Device > User Groups to create a group sslvpngroup with the member sslvpnuser1.
- Activate the mobile token.
- When the user sslvpnuser1 is created, an email is sent to the user's email address. Follow the instructions to install your FortiToken mobile application on your device and activate your token.
- Configure SSL VPN web portal.
- Go to VPN > SSL-VPN Portals to create a tunnel mode only portal my-split-tunnel-portal.
- Enable Split Tunneling.
- Select Routing Address.
- Configure SSL VPN settings.
- Go to VPN > SSL-VPN Settings.
- For Listen on Interface(s), select wan1.
- Set Listen on Port to 10443.
- Choose a certificate for Server Certificate. The default is Fortinet_Factory.
- In Authentication/Portal MappingAll Other Users/Groups, set the Portal to tunnel-access.
- Create new Authentication/Portal Mapping for group sslvpngroup mapping portal my-split-tunnel-portal.
- Configure SSL VPN firewall policy.
- Go to Policy & Objects > IPv4 Policy.
- Fill in the firewall policy name. In this example, sslvpn certificate auth.
- Incoming interface must be SSL-VPN tunnel interface(ssl.root).
- Set the Source Address to all and Source User to sslvpngroup.
- Set the Outgoing Interface to the local network interface so that the remote user can access the internal network. In this example, port1.
- Set Destination Address to the internal protected subnet 192.168.1.0.
- Set Schedule to always, Service to ALL, and Action to Accept.
- Enable NAT.
- Configure any remaining firewall and security options as desired.
- Click OK.
To configure SSL VPN using the CLI:
- Configure the interface and firewall address.
config system interface edit "wan1" set vdom "root" set ip 172.20.120.123 255.255.255.0 next end - Configure internal interface and protected subnet, then connect the port1 interface to the internal network.
config system interface edit "port1" set vdom "root" set ip 192.168.1.99 255.255.255.0 next endconfig firewall address edit "192.168.1.0" set subnet 192.168.1.0 255.255.255.0 next end - Register FortiGate for FortiCare Support.
To add or download a mobile token on FortiGate, FortiGate must be registered for FortiCare Support. If your FortiGate is registered, skip this step.
# diagnose forticare direct-registration product-registration -a "your account@xxx.com" -p "your password" -T "Your Country/Region" -R "Your Reseller" -e 1
- Add FortiToken mobile to FortiGate.
- If your FortiGate has FortiToken installed, skip this step.
execute fortitoken-mobile import <your FTM code>
- Every FortiGate has two free mobile Tokens. You can download the free token.
execute fortitoken-mobile import 0000-0000-0000-0000-0000
- If your FortiGate has FortiToken installed, skip this step.
- Configure user and user group.
config user local edit "sslvpnuser1" set type password set two-factor fortitoken set fortitoken <select mobile token for the option list> set email-to <user's email address> set passwd <user's password> next end config user group edit "sslvpngroup" set member "sslvpnuser1" next end - Activate the mobile token.
- When the user sslvpnuser1 is created, an email is sent to the user's email address. Follow the instructions to install your FortiToken mobile application on your device and activate your token.
- Configure SSL VPN web portal.
config vpn ssl web portal edit "my-split-tunnel-portal" set tunnel-mode enable set split-tunneling enable set split-tunneling-routing-address "192.168.1.0" set ip-pools "SSLVPN_TUNNEL_ADDR1" next end - Configure SSL VPN settings.
config vpn ssl settings set servercert "Fortinet_Factory" set tunnel-ip-pools "SSLVPN_TUNNEL_ADDR1" set tunnel-ipv6-pools "SSLVPN_TUNNEL_IPv6_ADDR1" set source-interface "wan1" set source-address "all" set source-address6 "all" set default-portal "full-access" config authentication-rule edit 1 set groups "sslvpngroup" set portal "my-split-tunnel-portal" next next end - Configure one SSL VPN firewall policy to allow remote user to access the internal network.
config firewall policy edit 1 set name "sslvpn web mode access" set srcintf "ssl.root" set dstintf "port1" set srcaddr "all" set dstaddr "192.168.1.0" set groups “sslvpngroup” set action accept set schedule "always" set service "ALL" set nat enable next end
To see the results of tunnel connection:
- Download FortiClient from www.forticlient.com.
- Open the FortiClient Console and go to Remote Access > Configure VPN.
- Add a new connection:
- Set VPN Type to SSL VPN.
- Set the connection name.
- Set Remote Gateway to the IP of the listening FortiGate interface, in this example, 172.20.120.123.
- Select Customize Port and set it to 10443.
- Save your settings.
- Log in using the sslvpnuser1 credentials.
- Enter the token from the FortiToken mobile app when required.
When the authentication is approved, sslvpnuser1 is logged into the SSL VPN tunnel and traffic to 192.168.1.0 goes through the tunnel. Other traffic goes through the local gateway.
To check the SSL VPN connection using the GUI:
- Go to VPN > Monitor > SSL-VPN Monitor to verify the user’s connection.
- Go to Log & Report > Forward Traffic to view the details of the SSL VPN traffic.
To check the web portal login using the CLI:
get vpn ssl monitor SSL VPN Login Users: Index User Auth Type Timeout From HTTP in/out HTTPS in/out 0 sslvpnuser1 1(1) 229 10.1.100.254 0/0 0/0 SSL VPN sessions: Index User Source IP Duration I/O Bytes Tunnel/Dest IP
To check the tunnel login using the CLI:
get vpn ssl monitor SSL VPN Login Users: Index User Auth Type Timeout From HTTP in/out HTTPS in/out 0 sslvpnuser1 1(1) 291 10.1.100.254 0/0 0/0 SSL VPN sessions: Index User Source IP Duration I/O Bytes Tunnel/Dest IP 0 sslvpnuser1 10.1.100.254 9 22099/43228 10.212.134.200

